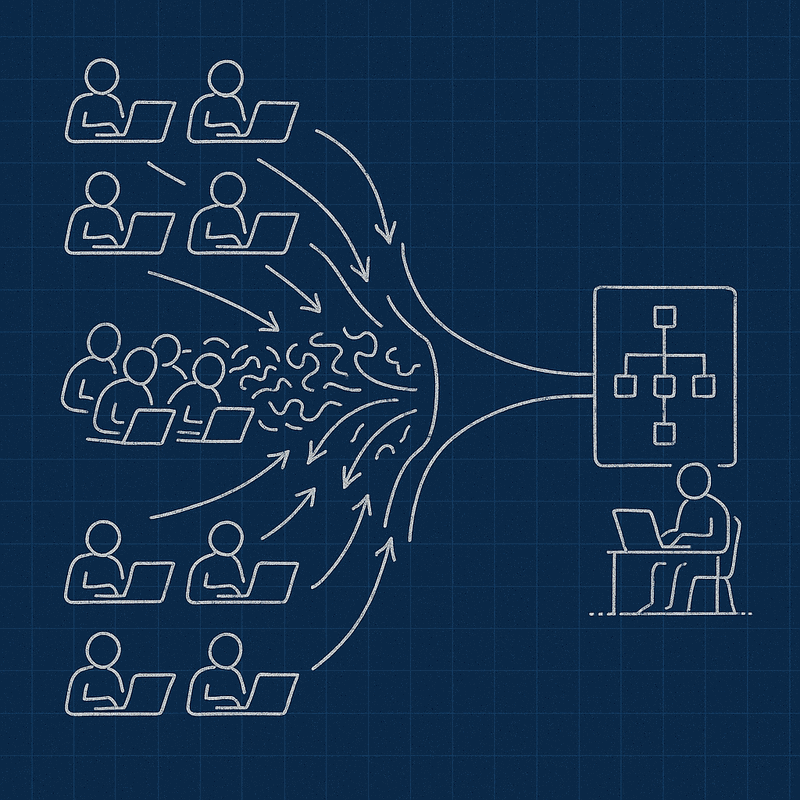
Four development teams. One platform team. Bi-weekly production deployments. Daily coordination meetings that solved nothing. Welcome to the enterprise architecture coordination crisis that plagues organizations worldwide—a crisis where technical excellence meets organizational dysfunction, and everyone loses.
I spent six months making this problem worse before discovering what actually worked. Not through more meetings, better communication tools, or motivational team-building exercises, but through systematic enterprise architecture governance that fundamentally changed how teams interact.
The stakes are higher than most architects realize. When enterprise architecture fails at team coordination, it is not just project dashboards that turn red. Citizens experience service disruptions. Business capabilities stagnate. Innovation grinds to a halt. Your organization hemorrhages talent as skilled professionals spend their days in coordination meetings instead of building value.
This article reveals how enterprise governance transforms coordination chaos into systematic capability—without adding more meetings, creating more bureaucracy, or forcing artificial team restructuring. You will learn the Architecture Governance Rule that eliminated 70% of coordination overhead and the three-level implementation framework that makes it work in practice.
The Hidden Cost of Team Coordination Failures
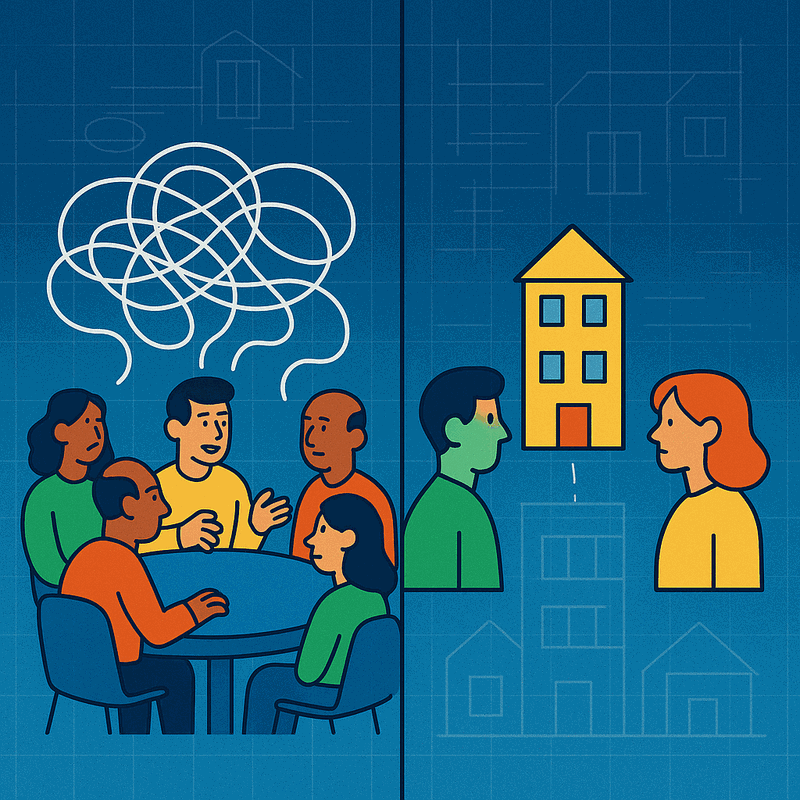
The coordination crisis rarely announces itself. It creeps into organizations through incremental complexity, each new team, system, and integration adding another thread to an increasingly tangled web. By the time leadership recognizes the problem, daily standups have become three-hour marathons where nothing gets decided.
The Four Symptoms of Coordination Breakdown
In my experience transforming a national-scale government platform, four symptoms consistently revealed deeper architectural problems:
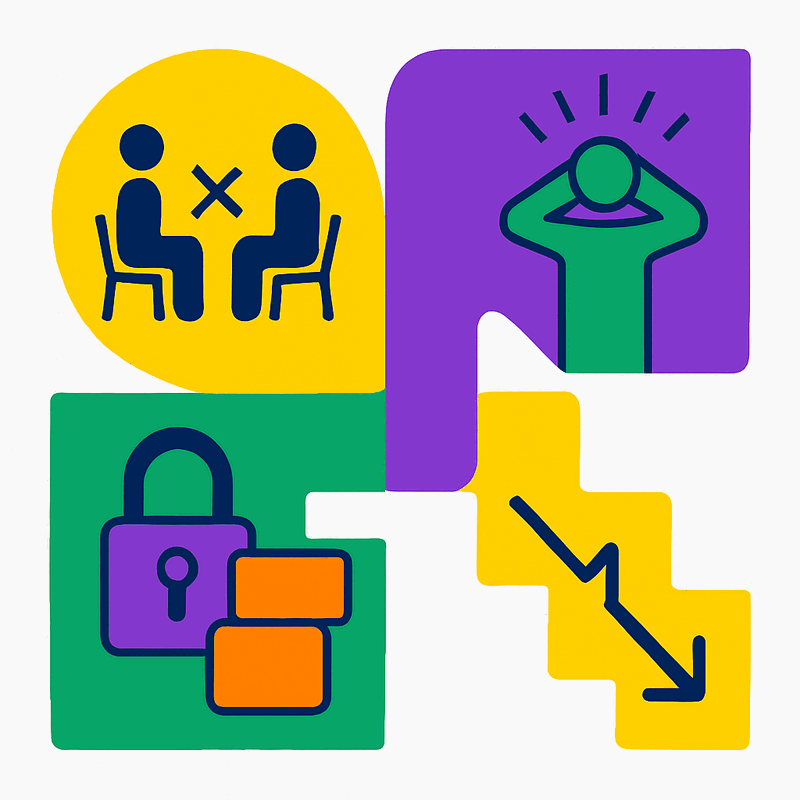
Daily coordination meetings that solved nothing. Teams gathered religiously every morning, discussed the same blockers, raised the same issues, and left with the same unresolved dependencies. The meetings became performative rather than productive—a ritual of shared frustration rather than problem-solving.
Platform team overwhelmed with manual integration work. What should have been a center of excellence for technical capability became a bottleneck for basic integration tasks. Every deployment required manual intervention. Every service connection needed custom configuration. The platform team spent 80% of their time on repetitive integration work instead of building reusable capabilities.
Development teams blocked waiting for deployment windows. Teams that should have been delivering value independently found themselves queued behind each other, waiting for shared resources, competing for deployment slots, and negotiating access to production environments. A simple feature that took two days to build required two weeks to deploy.
Twenty-five applications with no clear ownership boundaries. The most insidious symptom: nobody knew who owned what. Three teams mentioned the same API in their standups. Four teams claimed responsibility for customer data. Everyone assumed someone else maintained the authentication service. The lack of clear ownership created a responsibility vacuum where problems festered until they became crises.
The Real Problem: Architectural Governance, Not Communication
Most organizations respond to coordination chaos by improving communication. They implement new collaboration tools, schedule more alignment meetings, create RACI matrices, and hope that better information flow will solve the problem. It never does.
The real issue runs deeper than communication—it is an architectural governance problem masquerading as a people problem. Teams cannot coordinate effectively when the architecture itself lacks clear boundaries, standardized interfaces, and systematic governance. No amount of communication can compensate for architectural ambiguity.
Consider this scenario: Three teams need to modify the customer notification service. Team A thinks it owns the business logic. Team B built the original implementation. The platform team provides the infrastructure. Without architectural governance defining clear domain boundaries and decision rights, these teams will spend weeks in meetings negotiating who can change what. With proper governance, the decision takes minutes: the business domain owner makes business rule decisions, the platform team provides infrastructure services, and the implementation team maintains the code under business domain authority.
Common Misconceptions About Team Coordination
Misconception 1: More communication solves coordination problems. Communication is necessary but not sufficient. Without clear architectural boundaries, communication becomes negotiation. Teams spend time discussing what should be predetermined by governance.
Misconception 2: Cross-functional teams eliminate coordination needs. Cross-functional teams reduce some coordination but cannot eliminate the need for systematic governance. Even the best cross-functional team needs clear interfaces with other teams and systems.
Misconception 3: Microservices automatically improve team independence. Microservices without governance create distributed coordination problems. Teams become independent in deployment but dependent in everything else—data access, security policies, monitoring strategies.
Misconception 4: Agile methodologies solve coordination at scale. Agile practices work brilliantly within teams but break down between teams without architectural governance. Daily standups become coordination bottlenecks when teams lack clear boundaries.
The Architecture Governance Rule: Your Framework for Transformation
After six months of failed attempts at fixing coordination through traditional means, I discovered a principle that changed everything. I call it the Architecture Governance Rule:
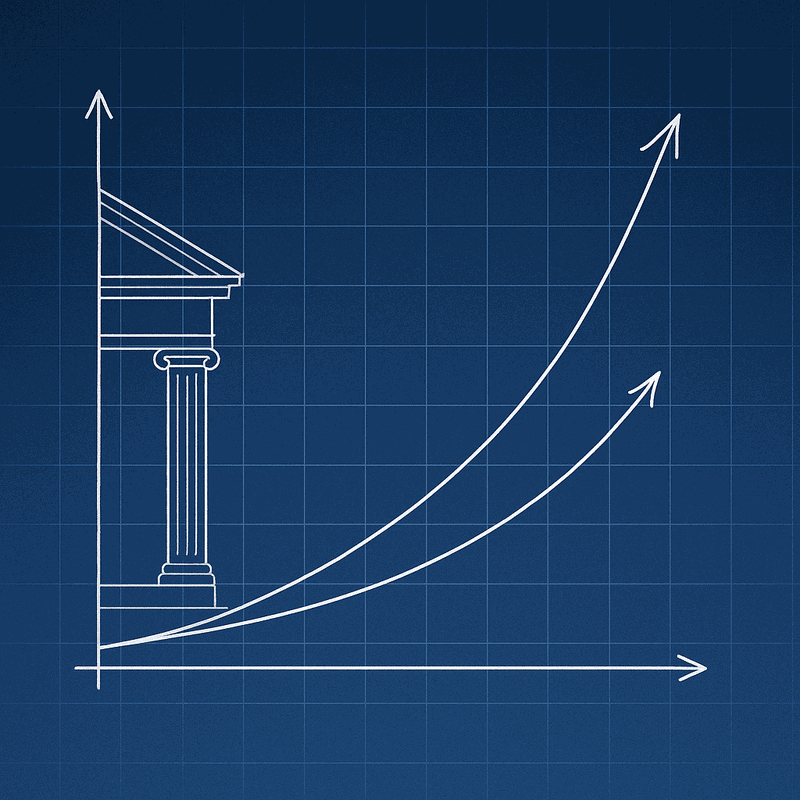
Manual coordination scales linearly with teams—add one team, add one meeting. Architecture governance scales exponentially with capability—design it once, every team benefits.
This rule reveals why adding more coordination mechanisms fails. Every new meeting, process, or communication channel adds linear overhead. Ten teams need forty-five potential coordination points. Twenty teams need one hundred ninety. The complexity explodes geometrically while your ability to manage it grows arithmetically.
Architecture governance inverts this dynamic. Instead of managing coordination points, you establish systematic capabilities that eliminate the need for coordination. Design clear domain boundaries once, and teams stop negotiating ownership. Implement standardized interfaces once, and integration becomes automatic. Define decision rights once, and escalation paths become clear.
The Mathematical Reality of Coordination Overhead
The mathematics of team coordination are unforgiving. In a team environment without governance:
- 2 teams: 1 coordination relationship
- 5 teams: 10 coordination relationships
- 10 teams: 45 coordination relationships
- 20 teams: 190 coordination relationships
Each coordination relationship requires meetings, documentation, and conflict resolution. The overhead grows exponentially while your management capacity grows linearly. This mathematical reality explains why large organizations without governance become coordination nightmares.
Architecture governance breaks this mathematical prison by eliminating the need for most coordination relationships. Teams interact through standardized interfaces rather than negotiated agreements.
The Four Enterprise Principles That Enable Governance
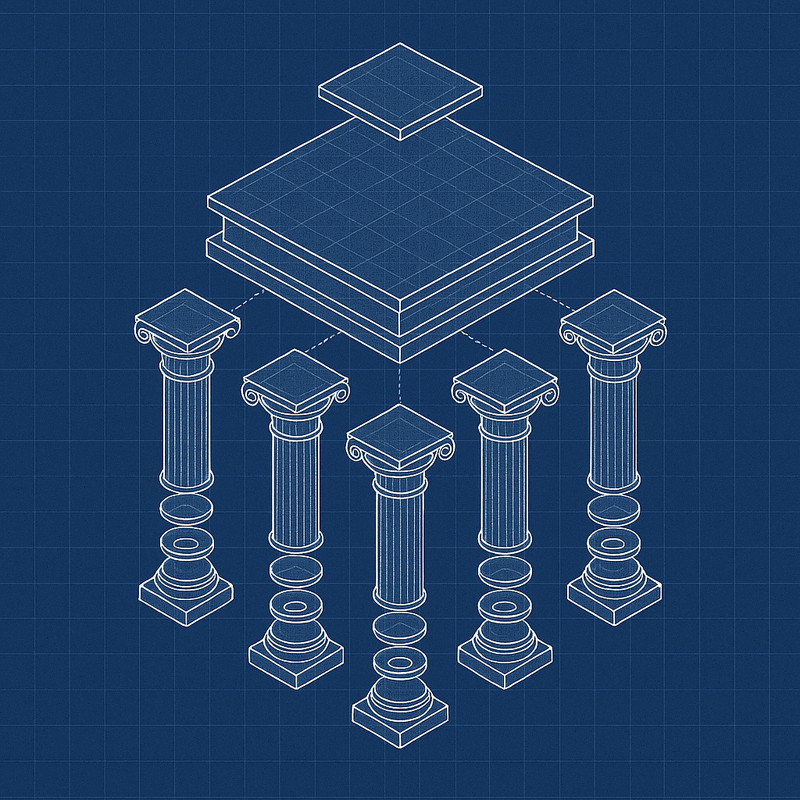
Effective architecture governance rests on four foundational principles, each addressing a specific aspect of team coordination:
Modularity: Teams operate independently within clear domain boundaries. Each team owns a clearly defined set of capabilities, makes autonomous decisions within their domain, and provides services to other teams through well-defined interfaces. Modularity transforms "who owns this?" from a political negotiation into an architectural decision.
Interoperability: Teams integrate through standardized interfaces. Instead of custom integrations for every team interaction, standardized patterns enable plug-and-play connectivity. APIs follow consistent conventions. Data formats align to enterprise standards. Integration becomes configuration rather than custom development.
Security: Enterprise-wide governance maintained across all teams. Security cannot be delegated or fragmented. A unified security architecture ensures consistent protection across all domains while enabling teams to operate independently within secure boundaries. Single sign-on, unified audit trails, and consistent authorization patterns eliminate security as a coordination bottleneck.
Agility: Architecture supports rapid business change. Business requirements change faster than organizational structures. The architecture must enable rapid reconfiguration without requiring team reorganization. Services can be recomposed, capabilities can be reassigned, and new requirements can be accommodated without architectural rebuild.
From Principles to Practice: The Dataset Example
These principles seem abstract until you see them in action. Let me share a concrete example that demonstrates their power.
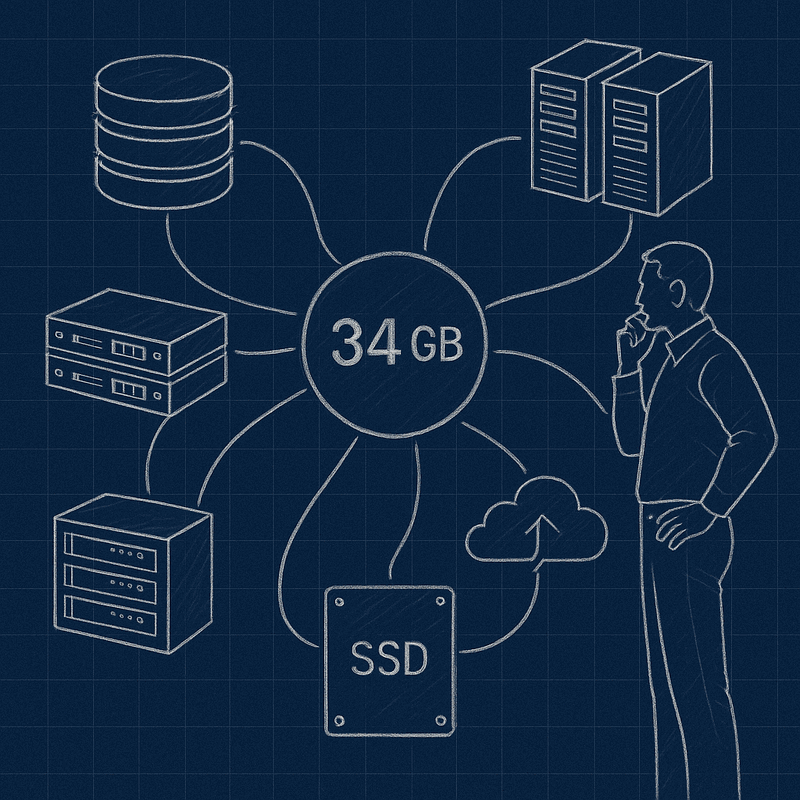
Our dataset inventory analysis revealed thirty-four gigabytes of critical data scattered across six different storage technologies. MongoDB held user profiles. PostgreSQL stored transactions. Elasticsearch indexed content. Redis cached sessions. File systems archived documents. Kafka streamed events. Each technology chosen by different teams for valid reasons, but the collective result was chaos.
Every business query required coordination across multiple teams. Backup strategies needed six different approaches. Data governance became impossible when nobody could answer "where is our customer data?" The dataset chaos created a coordination nightmare that consumed hours of meeting time daily.
Applying Modularity to Data Ownership
Before: Three teams claimed ownership of customer data. Marketing team owned "customer profiles." Sales team owned "customer contacts." Support team owned "customer cases." Nobody owned the complete customer domain.
After: Single customer domain team owned all customer-related data regardless of storage technology. Marketing accessed customer data through customer domain services. Sales accessed customer data through customer domain services. Support accessed customer data through customer domain services.
Implementing Interoperability for Data Access
Before: Each team accessed data directly through database connections. MongoDB queries in marketing code. PostgreSQL joins in sales applications. Elasticsearch aggregations in support tools. Every data access was custom integration.
After: Customer domain team provided standardized data services. GetCustomerProfile API. UpdateCustomerContact API. SearchCustomerHistory API. Teams accessed data through services, not direct database connections.
Establishing Security Governance
Before: Six different authentication mechanisms. Database credentials scattered across applications. Audit trails fragmented across storage systems. Security reviews required coordinating six teams.
After: Unified authentication and authorization. All data access through authenticated services. Centralized audit logging. Security governance through service interfaces rather than database access.
Enabling Agility Through Abstraction
Before: Changing storage technology required coordinating all consuming teams. Migrating from MongoDB to PostgreSQL meant updating marketing applications, sales tools, and support systems.
After: Customer domain team could change storage technologies without impacting consumers. Service interfaces remained stable while implementation evolved. Migration became domain-internal decision rather than enterprise coordination effort.
The result? The same thirty-four gigabytes of data, but zero coordination meetings about data access. Teams knew exactly who owned what, how to access it, and what they could change independently.
Three-Level Implementation: Making Governance Real
Understanding principles is one thing. Implementing them is another. Successful architecture governance requires coordinated action across three distinct levels, each with specific responsibilities and outcomes.
Enterprise Level: Establishing the Governance Framework
At the enterprise level, architecture governance establishes the framework within which all teams operate. This is not about central control—it is about enabling distributed decision-making within clear boundaries.
Clear Domain Ownership
Domain ownership defines who owns what capabilities. Not just systems or applications, but business capabilities. The customer domain team owns everything related to customer management, from data models to business rules to service interfaces. This ownership transcends organizational structure—even if team members change, the domain ownership remains clear.
Implementation Steps:
1. Map business capabilities to domains. Start with core business functions: customer management, order processing, inventory control, financial transactions.
2. Assign domain ownership to teams. Each domain has one owning team, regardless of how many systems implement the domain.
3. Define domain boundaries explicitly. Document what each domain owns, what it provides to others, and what it consumes from others.
4. Establish domain governance processes. How does the domain team make decisions? How do they communicate changes? How do they resolve conflicts?
Shared Architectural Principles
Shared principles ensure consistency without requiring coordination. When every team follows the same principles for API design, error handling, and logging, integration becomes predictable. Teams can build independently while knowing their services will work together.
Critical Principles to Establish:
- Service interface standards: REST API conventions, error response formats, authentication mechanisms
- Data governance standards: Data quality requirements, privacy controls, audit logging
- Deployment standards: Container specifications, environment configurations, monitoring requirements
- Security standards: Authentication patterns, authorization models, vulnerability management
Decision-Making Authority Distribution
Authority distribution empowers teams to move fast within their domains. The customer team does not need permission to change their data model. The order team does not need approval to optimize their workflows. Authority matches responsibility, eliminating approval bottlenecks.
Authority Distribution Framework:
- Domain internal decisions: Team has full autonomy (data models, business logic, implementation choices)
- Interface decisions: Team has autonomy with notification requirements (API changes, service level agreements)
- Cross-domain decisions: Requires escalation and agreement (shared data standards, security policies)
- Enterprise decisions: Requires architecture governance board (technology platform choices, compliance requirements)
Escalation Processes for Cross-Domain Coordination
Escalation processes handle the exceptional cases where coordination is genuinely required. Instead of everything requiring coordination, only true cross-domain changes trigger escalation. These processes are exception handlers, not standard operating procedure.
Three-Tier Escalation Model:
1. Domain Level: Teams resolve issues within their domain independently
2. Cross-Domain Level: Domain representatives negotiate agreements for shared concerns
3. Enterprise Level: Architecture governance board resolves conflicts that cannot be negotiated
Application Level: Defining Integration Patterns
The application level translates enterprise governance into concrete technical patterns. This is where abstract principles become actionable standards.
Team Application Portfolio Ownership
Each team owns a specific application portfolio. Not just applications they built, but applications within their domain. If customer management requires five applications, the customer domain team owns all five, regardless of who originally built them. This portfolio ownership eliminates the "orphan application" problem where nobody maintains critical systems.
Portfolio Definition Process:
1. Inventory existing applications by domain. Map every application to its primary business domain.
2. Assign portfolio ownership. Each domain team becomes responsible for all applications within their domain.
3. Establish maintenance responsibilities. Domain teams maintain applications they own, even if they did not build them.
4. Plan consolidation opportunities. Multiple applications serving the same domain often indicate consolidation opportunities.
Service Interface Standards
Teams provide services through defined interfaces. Your domain's capabilities are exposed as services that other teams consume. The interface is your contract with the enterprise. You can change anything behind the interface, but the interface itself requires governance. This separation of interface from implementation enables independent evolution.
Interface Standard Components:
- API Design Standards: RESTful conventions, resource naming, HTTP status codes
- Authentication Standards: OAuth 2.0, JWT tokens, service-to-service authentication
- Error Handling Standards: Error response formats, error codes, logging requirements
- Versioning Standards: Semantic versioning, backward compatibility requirements, deprecation policies
- Documentation Standards: OpenAPI specifications, usage examples, change notifications
Integration Enabling Autonomous Development
Integration standards enable autonomous development. Every team uses the same patterns for service discovery, authentication, error handling, and monitoring. New services automatically work with existing infrastructure. New teams immediately understand how to integrate. Standards become enablers, not constraints.
Integration Infrastructure Components:
- Service Discovery: Centralized registry of available services and their interfaces
- API Gateway: Unified entry point with authentication, authorization, and monitoring
- Message Broker: Asynchronous communication for event-driven patterns
- Monitoring Platform: Distributed tracing, metrics collection, alerting across all services
- Configuration Management: Environment-specific configurations, secrets management
Technology Level: Enabling Independence Through Platform Services
The technology level provides the platform capabilities that make independence possible. Without these foundational services, teams cannot operate autonomously regardless of governance structures.
Self-Service Deployment Capabilities
Self-service deployment eliminates the platform team as a deployment bottleneck. Teams deploy their own services, manage their own configurations, and control their own release cycles. The platform team provides the capability; teams use it independently.
Self-Service Platform Components:
- Container Orchestration: Kubernetes clusters with namespace isolation per team
- CI/CD Pipelines: Automated build, test, and deployment pipelines
- Infrastructure as Code: Terraform modules for common infrastructure patterns
- Environment Management: Automated provisioning of development, staging, and production environments
- Deployment Automation: Blue-green deployments, rollback capabilities, health checks
Container Orchestration
Container orchestration abstracts infrastructure complexity. Teams define what they need; the platform handles how it runs. Scaling, failover, and resource management become platform concerns, not team coordination points.
Orchestration Capabilities:
- Resource Isolation: CPU, memory, and storage quotas per team namespace
- Service Mesh: Network security, traffic management, observability between services
- Auto-Scaling: Horizontal pod autoscaling based on CPU, memory, or custom metrics
- High Availability: Multi-zone deployments, automatic failover, disaster recovery
- Security Controls: Pod security policies, network policies, image scanning
Monitoring and Logging
Monitoring and logging provide visibility without requiring coordination. Every team sees their services' health, performance, and errors. Standardized logging enables cross-team debugging without meetings. Problems become visible before they require escalation.
Observability Platform:
- Metrics Collection: Prometheus for application and infrastructure metrics
- Log Aggregation: Elasticsearch for centralized log storage and search
- Distributed Tracing: Jaeger for request flow across multiple services
- Alerting: Alert rules based on SLA violations, error rates, performance degradation
- Dashboards: Grafana dashboards for real-time visibility into system health
Infrastructure Services Consumption Model
Infrastructure services consumed rather than requested. Teams do not request databases—they provision them. They do not ask for message queues—they create them. Infrastructure becomes a service catalog, not a ticketing system.
Service Catalog Offerings:
- Database Services: PostgreSQL, MongoDB, Redis instances with backup and monitoring
- Message Services: Kafka topics, RabbitMQ queues with retention and scaling policies
- Storage Services: Object storage, file systems with encryption and access controls
- Networking Services: Load balancers, DNS entries, SSL certificates
- Security Services: Secret management, identity providers, certificate authorities
The Messy Reality of Implementation
On paper, this three-level implementation looks clean and logical. In practice, it is messy, political, and fraught with resistance. Let me share the reality of what implementation actually looks like.
The messiest negotiation in our transformation involved deciding who owned the "customer notification service." The business team claimed it because notifications were business rules. The platform team argued it was infrastructure. Development Team B insisted they owned it because they built it. Each had valid arguments. Each had political reasons for wanting ownership.
The governance framework forced the critical question: "Who makes decisions about notification rules?" The answer was clear: the business team. They owned the domain, even if they did not build the code or run the infrastructure.
But determining ownership was just the beginning. We then had to negotiate:
- How much autonomy did the business team have to change rules?
- What interface standards would the service follow?
- Who paid for the infrastructure costs?
- What happened when the service failed?
Each question required careful consideration of the three levels. Enterprise governance defined the ownership principle. Application architecture specified the interface standards. Technology platform provided the monitoring to detect failures.
The entire negotiation took four hours spread across two weeks. Without the governance framework, similar discussions had dragged on for months without resolution. The framework did not eliminate the complexity, but it provided a structured way to work through it.
Implementation Guide: Your Step-by-Step Approach
Implementing architecture governance cannot happen overnight, but it can begin immediately with a systematic approach. Here is the step-by-step methodology I used to transform team coordination from crisis to capability.
Phase 1: Assessment and Foundation (Weeks 1-4)
Week 1: Coordination Pain Point Inventory
Objective: Identify and catalog all coordination pain points across teams.
Activities:
1. Interview team leads from each development team, platform team, and business stakeholders
2. Document coordination meetings - frequency, duration, participants, outcomes
3. Map dependencies between teams, applications, and data sources
4. Identify bottlenecks where decisions or deployments get blocked
5. Catalog ownership conflicts where multiple teams claim or disclaim responsibility
Deliverable: Coordination Pain Point Register with prioritized list of issues
Week 2: Current State Architecture Mapping
Objective: Create comprehensive map of current architectural landscape.
Activities:
1. Application inventory with ownership assignments (current and disputed)
2. Data flow mapping between applications and teams
3. Integration pattern analysis - how do teams currently integrate?
4. Decision-making process documentation - who decides what, when, how?
5. Technology platform audit - what shared services exist or are missing?
Deliverable: Current State Architecture Document with visual maps
Week 3: Domain Boundary Definition
Objective: Establish clear domain boundaries based on business capabilities.
Activities:
1. Business capability modeling using techniques like capability mapping
2. Domain boundary workshops with business and technical stakeholders
3. Domain ownership assignment - one team per domain
4. Interface identification - what each domain exposes to others
5. Governance model design - how will domains make decisions?
Deliverable: Domain Model with clear boundaries and ownership assignments
Week 4: Quick Wins Identification
Objective: Identify immediate improvements that can be implemented quickly.
Activities:
1. Low-hanging fruit analysis - coordination problems with simple solutions
2. Pilot domain selection - choose one domain for initial implementation
3. Success metrics definition - how will you measure improvement?
4. Implementation roadmap - what happens in the next 12 weeks?
5. Stakeholder communication plan - how will you keep everyone informed?
Deliverable: Implementation Roadmap with quick wins and success metrics
Phase 2: Pilot Implementation (Weeks 5-8)
Pilot Domain Deep Dive
Select one domain for intensive governance implementation. Choose based on:
- High coordination pain - problems everyone recognizes
- Clear business value - improvements that matter to stakeholders
- Manageable scope - can be addressed in 4 weeks
- Willing team - domain team committed to the transformation
Week 5-6: Domain Governance Establishment
1. Formalize domain ownership with clear responsibilities and authority
2. Define domain interfaces using OpenAPI specifications
3. Establish domain decision-making process with escalation paths
4. Create domain service catalog listing all capabilities provided to other domains
5. Implement basic monitoring to track domain health and usage
Week 7-8: Interface Standardization
1. Migrate integrations to use standardized domain interfaces
2. Implement authentication and authorization for domain services
3. Add comprehensive logging for all domain interactions
4. Create domain documentation with usage examples and change processes
5. Establish SLA monitoring to track domain service performance
Phase 3: Scaling and Optimization (Weeks 9-12)
Platform Capabilities Development
Week 9-10: Self-Service Infrastructure
1. Deploy container orchestration platform (Kubernetes with team namespaces)
2. Implement CI/CD pipelines for automated deployment
3. Create infrastructure as code templates for common patterns
4. Establish monitoring and alerting across all teams and services
5. Provide self-service database and message queue provisioning
Week 11-12: Governance Process Refinement
1. Expand governance model to additional domains based on pilot learnings
2. Establish architecture review board for cross-domain decisions
3. Create governance documentation and training materials
4. Implement change management processes for interface evolution
5. Measure and communicate results from the transformation
Common Implementation Pitfalls and Solutions
Pitfall 1: Attempting Big Bang Implementation
Problem: Trying to implement governance across all teams simultaneously
Solution: Start with pilot domain, prove value, then expand systematically
Pitfall 2: Focusing Only on Technology
Problem: Implementing platform capabilities without addressing organizational governance
Solution: Balance technical and organizational changes, ensure domain ownership is clear
Pitfall 3: Ignoring Political Dynamics
Problem: Treating governance as purely technical problem, ignoring organizational politics
Solution: Acknowledge politics, build coalitions, demonstrate value before expanding
Pitfall 4: Creating Governance Bureaucracy
Problem: Adding approval processes that slow down development
Solution: Focus on enabling autonomy, not controlling decisions
Pitfall 5: Insufficient Monitoring and Measurement
Problem: Cannot demonstrate improvement or identify remaining issues
Solution: Establish baseline metrics, track progress weekly, communicate results
Measuring Success: From Crisis to Capability
Six months after implementing systematic architecture governance, the transformation was undeniable. But measuring success in enterprise architecture requires looking beyond traditional IT metrics to understand business impact.
Quantitative Improvements
70% reduction in coordination overhead. We went from fifteen coordination meetings per week to four. The eliminated meetings were not canceled—they simply became unnecessary. Teams stopped scheduling them when they no longer had coordination issues to discuss.
Measurement Method: Weekly calendar audit counting meetings with "coordination," "alignment," or "dependency" in title or agenda.
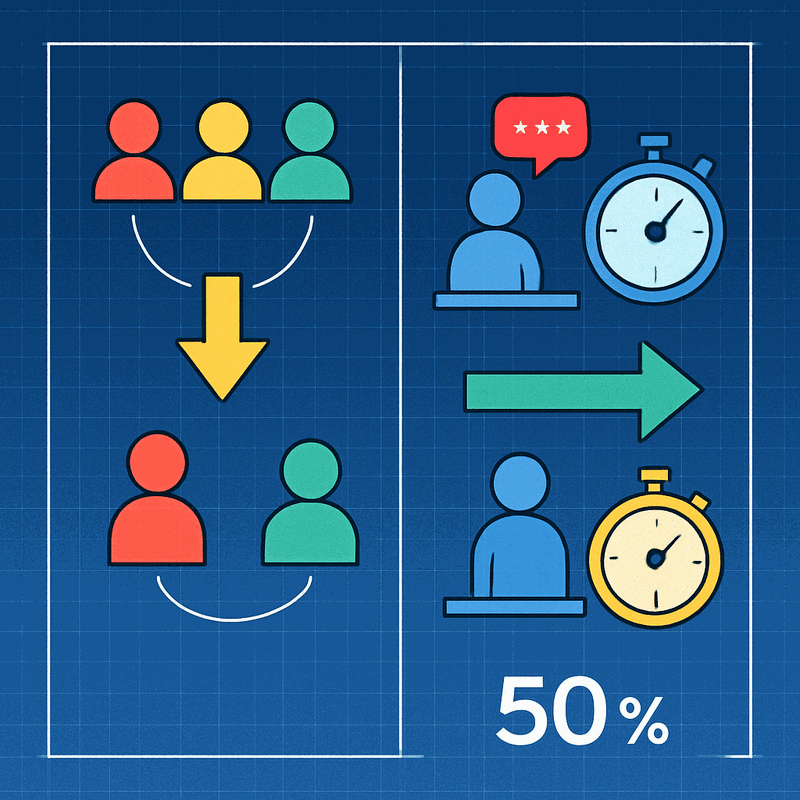
50% faster decision-making cycles. Decisions that previously required three weeks of cross-team negotiation now took days. Clear domain ownership eliminated the "who decides?" delay. Defined escalation paths streamlined cross-domain decisions.
Measurement Method: Decision tracking log measuring time from issue identification to resolution implementation.
85% reduction in production incidents requiring coordination. When services have clear owners and interfaces, failures become domain problems rather than coordination crises. Teams fix their own issues without emergency war rooms.
Measurement Method: Incident classification tracking whether resolution required cross-team coordination.
3x improvement in deployment frequency. Teams went from bi-weekly shared deployment windows to multiple daily independent deployments. The platform team stopped being a bottleneck and became an enabler.
Measurement Method: Deployment pipeline metrics tracking frequency and lead time per team.
Qualitative Transformations
Numbers tell only part of the story. The cultural transformation was equally significant:
Teams gained genuine autonomy. Not the false autonomy of "you own it but check with everyone," but real decision-making power within clear boundaries. Developers stopped asking permission and started shipping features.
Architecture became an enabler rather than a constraint. Teams saw architecture governance as something that helped them move faster, not bureaucracy that slowed them down. They actively participated in governance because it served their needs.
Innovation accelerated. With coordination overhead removed, teams had time and energy for innovation. They experimented with new technologies, optimized their services, and delivered capabilities nobody had requested because nobody thought they were possible.
Trust replaced negotiation. Teams trusted that others would maintain their interfaces, honor their contracts, and operate within boundaries. This trust eliminated the defensive behaviors that created coordination overhead in the first place.
Business Impact Metrics
Customer satisfaction scores improved 23%. Faster feature delivery and fewer service disruptions directly improved user experience. Customer support tickets decreased as teams could resolve issues faster without coordination delays.
Employee satisfaction scores improved 31%. Developers reported higher job satisfaction when spending time building features instead of attending coordination meetings. Team retention improved as talented engineers stopped leaving due to coordination frustration.
Time to market decreased 45%. New features reached customers faster when teams could develop and deploy independently. Business stakeholders could see their requirements implemented without waiting for cross-team coordination.
Technical debt decreased 38%. Teams could address technical debt within their domains without requiring coordination. Refactoring became routine domain improvement rather than enterprise-wide project requiring multiple team coordination.
The Unexpected Benefits
Some benefits surprised even me:
Security posture improved significantly. Standardized interfaces made security reviews easier. Centralized authentication and authorization eliminated security gaps between team integrations. Audit compliance became automated rather than manual process requiring coordination across teams.
Onboarding time dropped dramatically. New team members understood their domain, their boundaries, and their interfaces within days instead of months. The architecture governance framework became the best onboarding document we never had to write.
Business stakeholders engaged more effectively. When business owns domains rather than IT owning systems, business stakeholders became active participants rather than requirements sources. They understood their authority and used it to drive value.
Vendor management became strategic. With clear domain boundaries and interface standards, vendor selection and management became domain-level decisions. Teams could choose best-of-breed tools within their domains without requiring enterprise-wide coordination.
Your Next Step: Starting the Transformation
You do not need six months or a massive transformation program to begin improving team coordination through architecture governance. You can start this week with a single concrete action.
Take one recurring cross-team escalation—something that repeatedly causes coordination meetings—and analyze it through three levels:
Enterprise Level Question: Is this a governance issue? Who should own this capability? What principle would prevent this escalation? How should decision rights be distributed?
Application Level Question: Is this a boundary issue? Are domain boundaries unclear? Do services lack proper interfaces? Are integration patterns inconsistent?
Technology Level Question: Is this a platform issue? Do teams lack necessary platform services? Are infrastructure capabilities creating bottlenecks? Is deployment independence compromised?
Most coordination problems reveal themselves at one specific level. A customer data access issue might be an enterprise governance problem (unclear ownership). A service integration failure might be an application boundary problem (missing interface standards). A deployment bottleneck might be a technology platform problem (lacking self-service capabilities).
Once you identify the level causing coordination overhead, design one specific change at that level. Do not try to solve everything—fix one concrete problem:
- If it is a governance issue, define ownership for one domain
- If it is a boundary issue, standardize one interface pattern
- If it is a platform issue, implement one self-service capability
Start small, prove value, then expand. Each successful elimination of coordination overhead builds momentum for broader transformation.
Remember the Architecture Governance Rule: stop scaling coordination linearly; start scaling governance exponentially. The coordination meetings that consumed your week are symptoms, not the disease. The disease is architectural ambiguity that forces teams to coordinate what should be independent.
Your teams are not failing at coordination. Your architecture is failing to make coordination unnecessary.
Watch the video for the personal stories behind this framework: Enterprise Architecture - The Team Coordination Crisis
What coordination problem is consuming your team's time right now? Share in the comments below.
Continue Reading
Want the personal story behind this framework? This article is the comprehensive implementation guide. For the shorter personal narrative of how I discovered the Architecture Governance Rule, read:
Enterprise Architecture Governance: How I Stopped Making Team Coordination Worse →
Related articles: